Tenable Identity Exposure: Secure Active Directory and Eliminate Attack Paths
Tenable Identity Exposure: Secure Active Directory and Eliminate Attack Paths
- Assess your current state of zero trust with best practices for preventative identity security.
- Unified view of identities across on-prem and cloud-based AD deployments.
- Extended support for public and hybrid cloud Entra ID deployments.
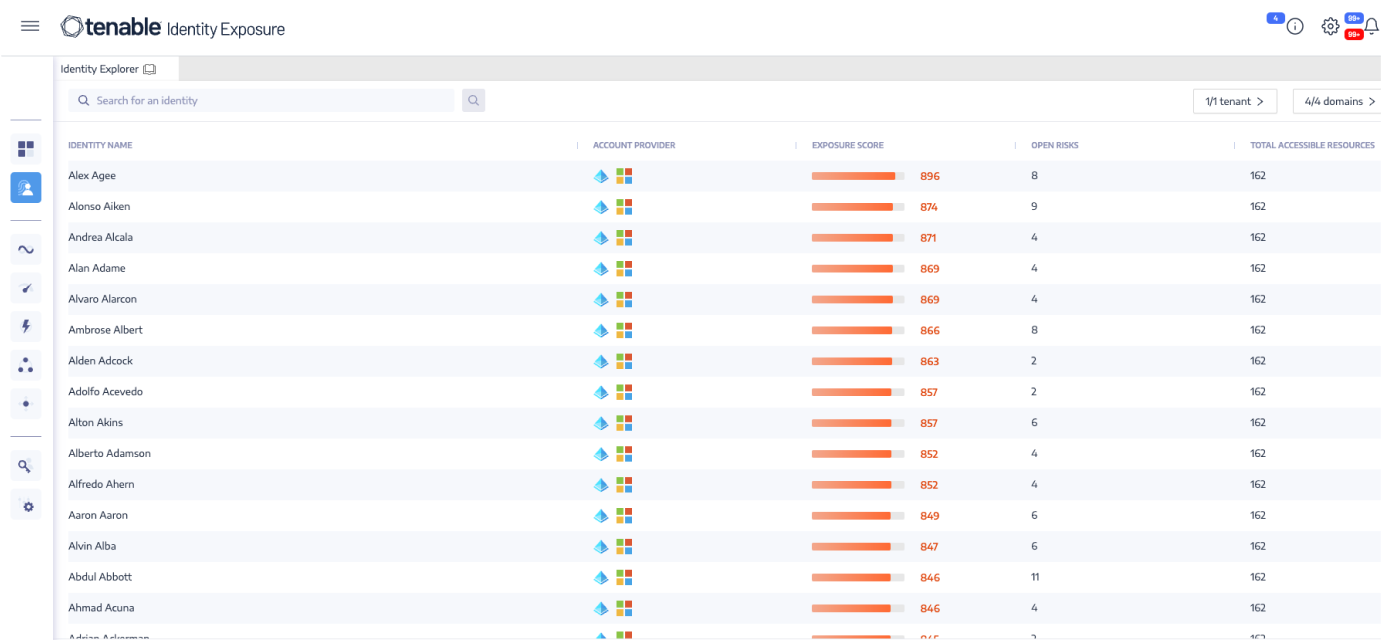
- Exposure management based on calculated Identity Risk Scores, focusing on areas of highest risk.
- Continuous validation and assessment of AD for attack prevention and detection.
REQUEST A DEMO
Tenable Customers - 60% of the Fortune 500 Trust Tenable
With Tenable Identity Exposure, you'll always have:
Tenable Identity Exposure Benefits
With Tenable Identity Exposure, you'll always have:
Identity Unification and AI‑Driven Risk Scoring
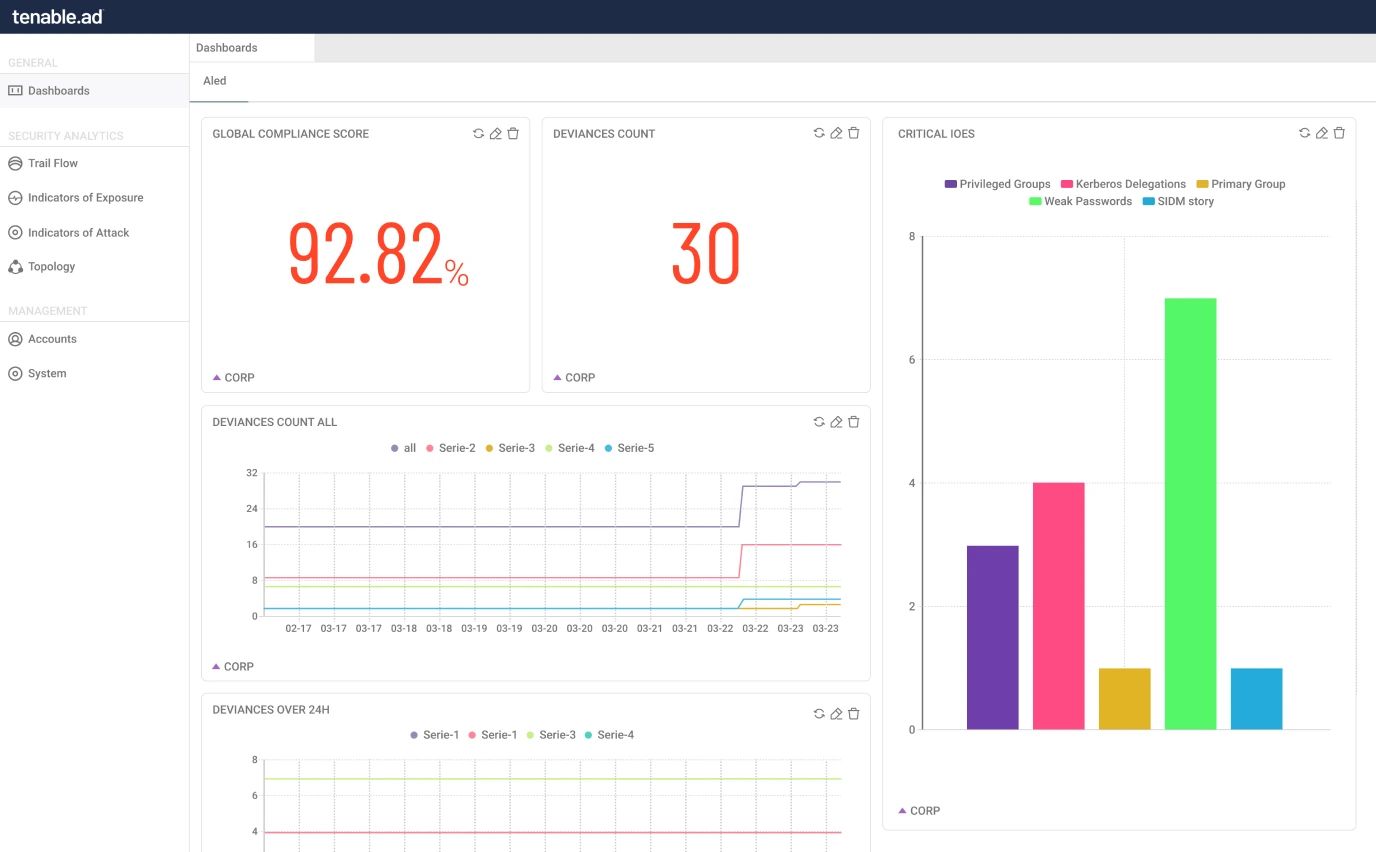
Unify Active Directory, hybrid, and Entra ID accounts all in a single view. Gain control of identities dispersed between multiple directory services, domains, and forests in one place. Each identity is scored by our data science and AI engine, which ranks identities based on the level of risk should that identity be compromised.
Expand
Continually Assess Directory Services Security in Real‑Time
Assess the security posture of your directory services and uncover vulnerabilities, risky configurations, and permissions creep. Tenable Identity Exposure provides a step-by-step tactical guide that identifies affected objects, eliminating the need for time-consuming manual reports or scripts.
Expand
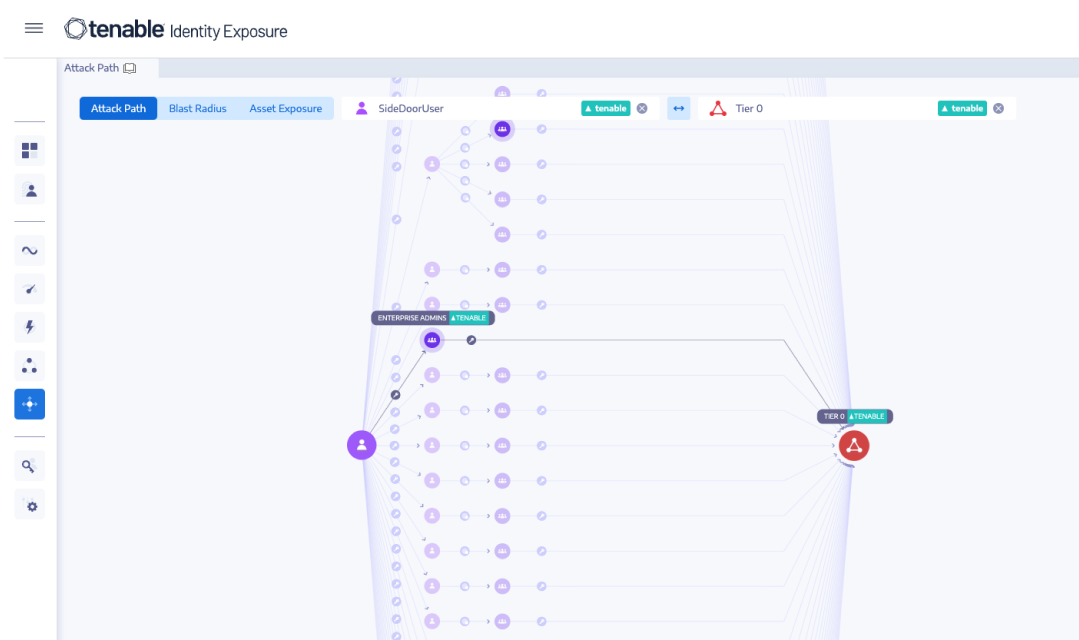
Eliminate Attack Paths that Lead to Domain Domination
Make sense of the complex interrelationships between objects, principals, and permissions, and eliminate attack paths that lead to domain dominance. Attack path analysis surfaces all the possible steps that attackers could take to move laterally, escalate privileges, and gain control over your enterprise directory services.
Expand
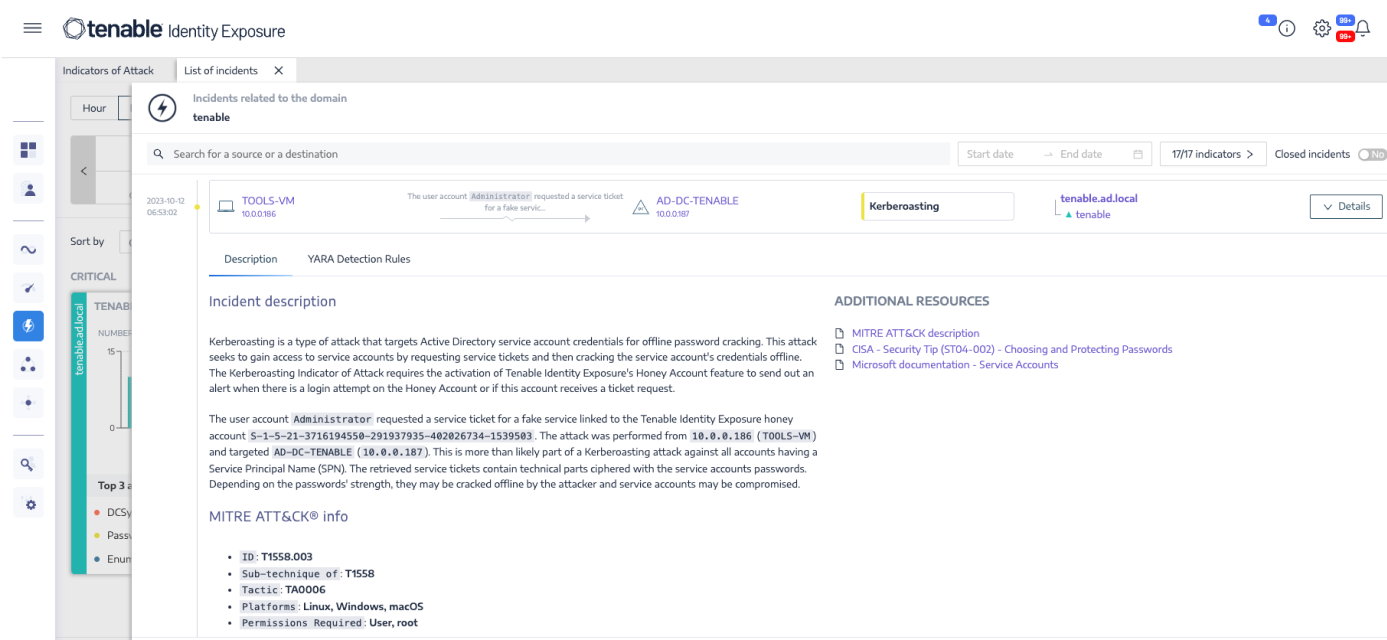
Real‑Time Attack Detection
Receive instant alerting against attacks including credential dumping, Kerberoasting, DCSync, ZeroLogon, and many more. Respond to attacks in real time by integrating Tenable Identity Exposure with your SIEM and SOAR. Tenable’s research team regularly updates indicators of attack as new identity-based exploits are discovered.
Expand
Investigate and Inform
Reduce incident response time and capture all changes to Active Directory using Trail Flow. Inform your incident response teams and enrich your security operations processes with real-time prioritization and detailed remediation steps.
Expand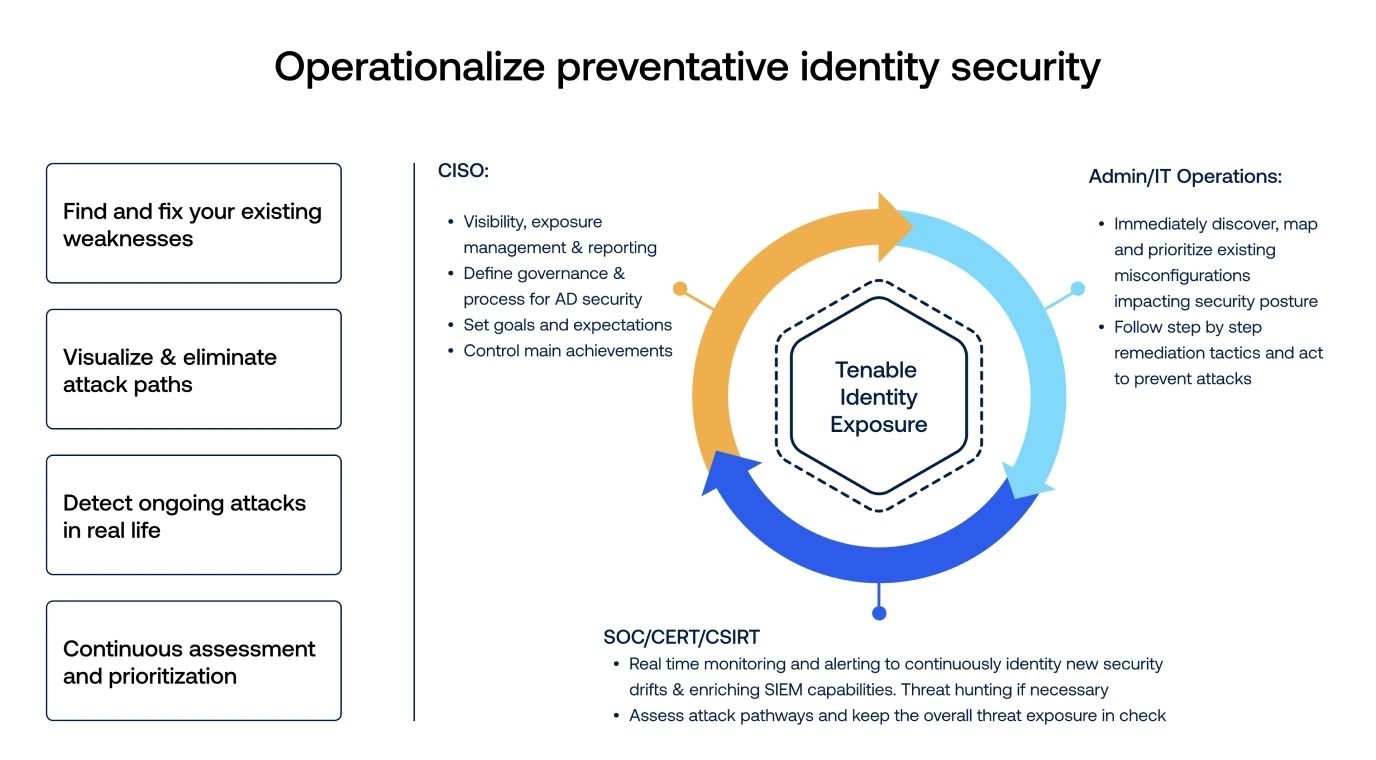
Introduction to Tenable Identity Exposure and Identity Aware Exposure Management
A quick walkthrough of Tenable Identity Exposure highlighting why Identity aware exposure management provides critical context to prioritize cyber security remediation efforts
Continuously detect
and prevent Active Directory attacks
-
No Agents. No Privileges.
No DelaysPrevents and detects sophisticated Active Directory attacks without agents and privileges.
-
Clouds Covered
Extended support for protecting public and hybrid cloud Azure Active Directory deployments and managing cloud identity risk with Indicators of Exposure specific to Azure AD.
-
Deployed Anywhere
Tenable Identity Exposure provides the flexibility of two architectural designs. On-prem to keep your data on-site and under your control. SaaS, so you can leverage the cloud.